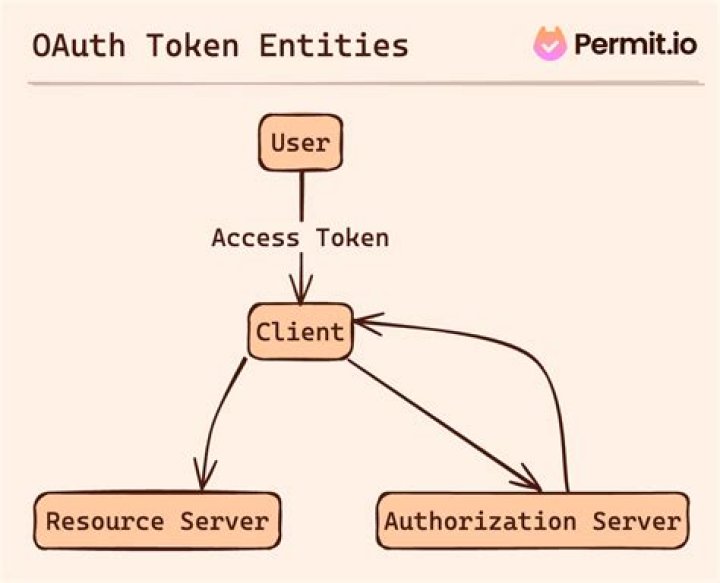
OAuth doesn’t share password data but instead uses authorization tokens to prove an identity between consumers and service providers. OAuth is an authentication protocol that allows you to approve one application interacting with another on your behalf without giving away your password.
How do authentication tokens work?
Token based authentication works by ensuring that each request to a server is accompanied by a signed token which the server verifies for authenticity and only then responds to the request.
What is an OAuth access token?
An OAuth Access Token is a string that the OAuth client uses to make requests to the resource server. … Access tokens do not convey user identity or any other information about the user to the OAuth client. Access tokens should only be used to make requests to the resource server.
How are OAuth tokens generated?
You use the client ID and one private key to create a signed JWT and construct an access-token request in the appropriate format. Your application then sends the token request to the Google OAuth 2.0 Authorization Server, which returns an access token. The application uses the token to access a Google API.How do I generate a token?
- In Admin Center, click the Apps and integrations icon ( ) in the sidebar, then select APIs > Zendesk APIs.
- Click the Settings tab, and make sure Token Access is enabled.
- Click the Add API token button to the right of Active API Tokens. …
- Enter an API token description.
Can OAuth token be stolen?
Adversaries can steal user application access tokens as a means of acquiring credentials to access remote systems and resources. … Adversaries can leverage OAuth authorization by constructing a malicious application designed to be granted access to resources with the target user’s OAuth token.
Why do we use tokens?
A token is used to make security decisions and to store tamper-proof information about some system entity. While a token is generally used to represent only security information, it is capable of holding additional free-form data that can be attached while the token is being created.
Where are OAuth tokens stored?
Tokens received from OAuth providers are stored in a Client Access Token Store. You can configure client access token stores under the Libraries > OAuth2 Stores node in the Policy Studio tree view.Where is refresh token stored?
You may store your tokens in a cookie, but that also can be accessed if the UA does not respect common security norms. You can store your tokens in local storage if it is implemented and provided by the UA, yet again if it respects the norms.
How does refresh token work?To use the refresh token, make a POST request to the service’s token endpoint with grant_type=refresh_token , and include the refresh token as well as the client credentials if required.
Article first time published onHow long does an OAuth token last?
By default, access tokens are valid for 60 days and programmatic refresh tokens are valid for a year. The member must reauthorize your application when refresh tokens expire.
How do I get my GitHub OAuth token?
- Navigate to your Git account settings, then Developer Settings. Click the Personal access tokens menu, then click Generate new token.
- Select repo as the scope. The token will be applicable for all the specified actions in your repositories.
- Click Generate Token.
Does token expire?
The access tokens may last anywhere from the current application session to a couple weeks. When the access token expires, the application will be forced to make the user sign in again, so that you as the service know the user is continually involved in re-authorizing the application.
How do handle tokens expire?
- Check if the token has expired. If the token is expired we clean up the existing token, application state and redirect the user to the login page.
- Request the resource with a valid token expiring in the future.
- Receive the resource.
Is JWT the same as OAuth?
Basically, JWT is a token format. OAuth is an standardised authorization protocol that can use JWT as a token. OAuth uses server-side and client-side storage. If you want to do real logout you must go with OAuth2.
Is token based authentication stateless?
Token-based authentication is stateless. We are not storing any information about our user on the server or in a session. … Application provides a signed token to the client. Client stores that token and sends it along with every request.
How do I protect my OAuth token?
- Use Proof Key for Code Exchange (PKCE) when dealing with authorization grant flows;
- Use Dynamic Attestation Protection with a secure authorization middleman service when dealing with authorization grant flow;
- Not store the OAuth app credentials in the source code or elsewhere;
What is token in API?
An API token is similar to a password and allows you to authenticate to Dataverse Software APIs to perform actions as you. Many Dataverse Software APIs require the use of an API token. … Passing Your API Token as an HTTP Header (Preferred) or a Query Parameter.
What if refresh token is stolen?
If the refresh token can be stolen, then so can the access token. With such an access token, the attacker can start making API calls. To make matters even more complicated, access tokens are often self-contained JWT tokens. Such tokens contain all the information needed for the API to make security decisions.
What if bearer token is stolen?
Because JWTs are used to identify the client, if one is stolen or compromised, an attacker has full access to the user’s account in the same way they would if the attacker had instead compromised the user’s username and password.
Can JWT be decoded?
A valid JWT can consist of just the header and payload sections. … By design, anyone can decode a JWT and read the contents of the header and payload sections. But we need access to the secret key used to create the signature to verify a token’s integrity.
How do I keep token safe?
To keep them secure, you should always store JWTs inside an httpOnly cookie. This is a special kind of cookie that’s only sent in HTTP requests to the server. It’s never accessible (both for reading or writing) from JavaScript running in the browser.
What is the best way to store token?
We strongly recommend that you store your tokens in local storage/session storage or a cookie.
How can I store oauth tokens in database?
1 Answer. A solution for this is to encrypt the data before is saved into the database and decrypt it each time you need to access it. In your case I think that symmetric encryption is the correct choice, thus you will need to have a private key that must be kept safe at all times.
Should you encrypt OAuth tokens?
It should be securely stored and encrypted. You should only store those tokens that are necessary for your application to function alongside your codebase.
Should you encrypt access tokens?
If you believe you can protect the encryption key better than the database storage/access, e.g. by using an HSM or secure file storage, then it makes sense to encrypt the token with such a key before storing it.
Should I Store API token in database?
Is it bad to store access tokens unhashed in the database? Yes and no. By storing tokens instead of user passwords, you have removed the danger of exposing a users password that he/she may have reused for multiple sites to an attacker. So it is definitely not as bad as storing passwords unhashed.
How do I know if my OAuth token is expired?
- convert expires_in to an expire time (epoch, RFC-3339/ISO-8601 datetime, etc.)
- store the expire time.
- on each resource request, check the current time against the expire time and make a token refresh request before the resource request if the access_token has expired.
How check expired OAuth token in C#?
The easiest way is to just try to call the service with it. It will reject it if it is expired and then you can request a new one. You can also keep the time you received the token and use the expires_in to calculate when it will approximately expire.
What is difference between refresh token and access token?
Refresh Token are typically longer lived than Access Tokens and used to request a new Access Token without forcing user authentication. Unlike Access Tokens, Refresh Tokens are only used with the Authorization Server and are never sent to a web service.
Is OAuth slow?
OAuth token refresh response is sometimes slow (up to 95 seconds!) We’re seeing instances of calls to refresh OAuth tokens that are taking longer to process. The worst one looks to be around 95 seconds to get a response back from the server.